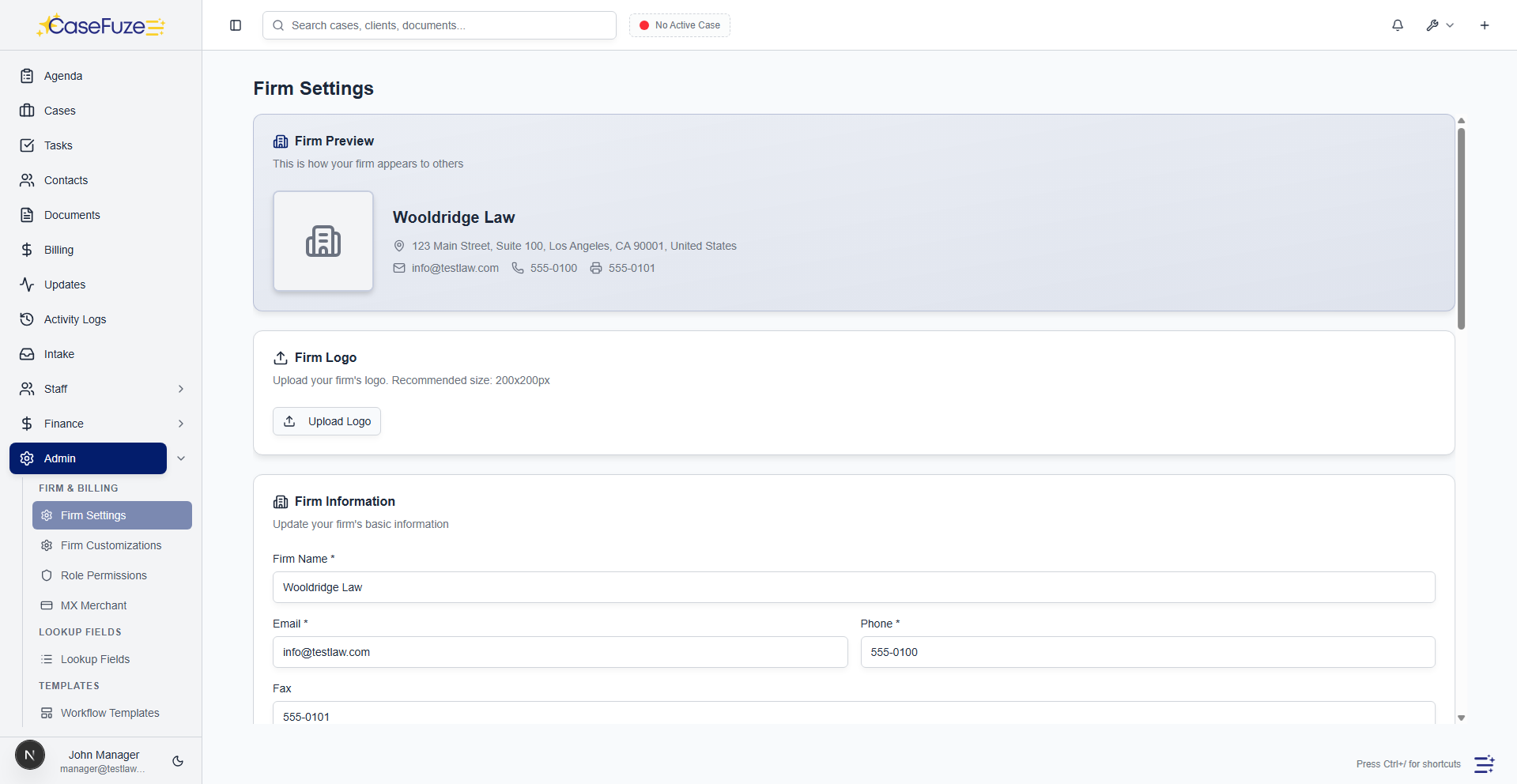
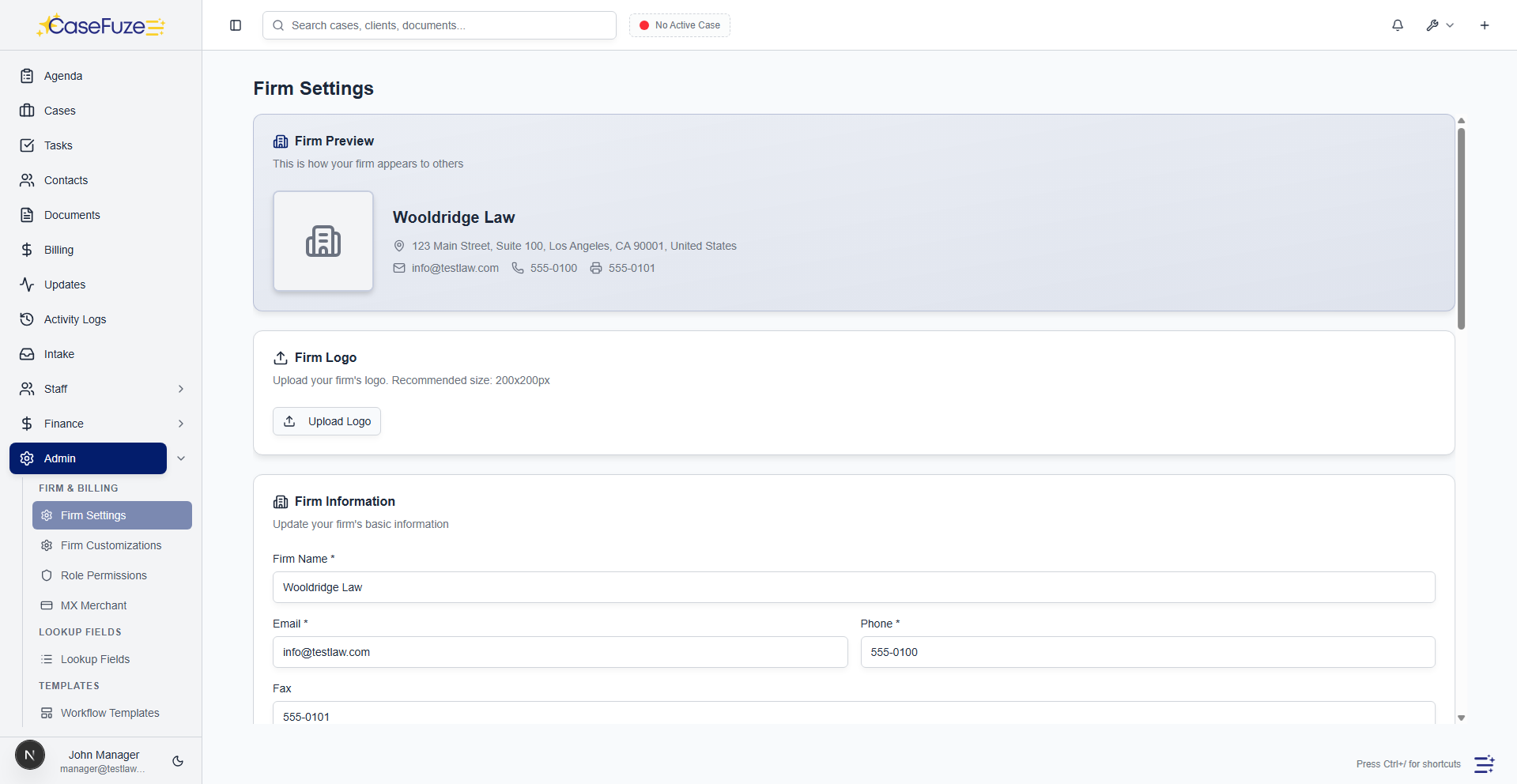
Security and Compliance That Protects Your Firm
Law firms handle sensitive information. Client confidences, medical records, financial data, trade secrets, personal details. One data breach destroys client trust, triggers bar complaints, and creates massive liability. Security isn't optional or something you can address later. It's foundational. CaseFuze is built with security at its core, not added as an afterthought.
SOC 2 Compliance
SOC 2 (Service Organization Control 2) is the gold standard for security auditing in cloud software.
- Security (protection from unauthorized access)
- Availability (system uptime and reliability)
- Processing integrity (accurate and complete processing)
ABA Technology Guidelines
The American Bar Association publishes technology guidelines for law firms covering data security, client confidentiality, and technology competence requirements.
- Encrypted communication channels for client data
- Access controls limiting data exposure
- Audit trails documenting system access and changes
HIPAA Considerations
Law firms handling medical records in personal injury, disability, or medical malpractice cases become HIPAA business associates.
- Encryption of stored and transmitted data
- Access controls limiting who sees medical records
- Audit logging of document access
Backup and Disaster Recovery
Data loss scenarios include more than hackers and breaches.
- CaseFuze maintains multiple backup levels:
- Real-time replication copies data to multiple servers simultaneously.
- If one server fails, others continue operating without data loss.
Uptime and Availability
Case management software that's down is useless.
- CaseFuze maintains 99.9% uptime, which translates to less than 9 hours of downtime per year (and most of that is planned maintenance during off-hours).
- Redundant infrastructure, load balancing, and automatic failover keep the system available even when individual components fail.
- Planned maintenance happens during low-usage periods (typically late night or weekends) with advance notification.
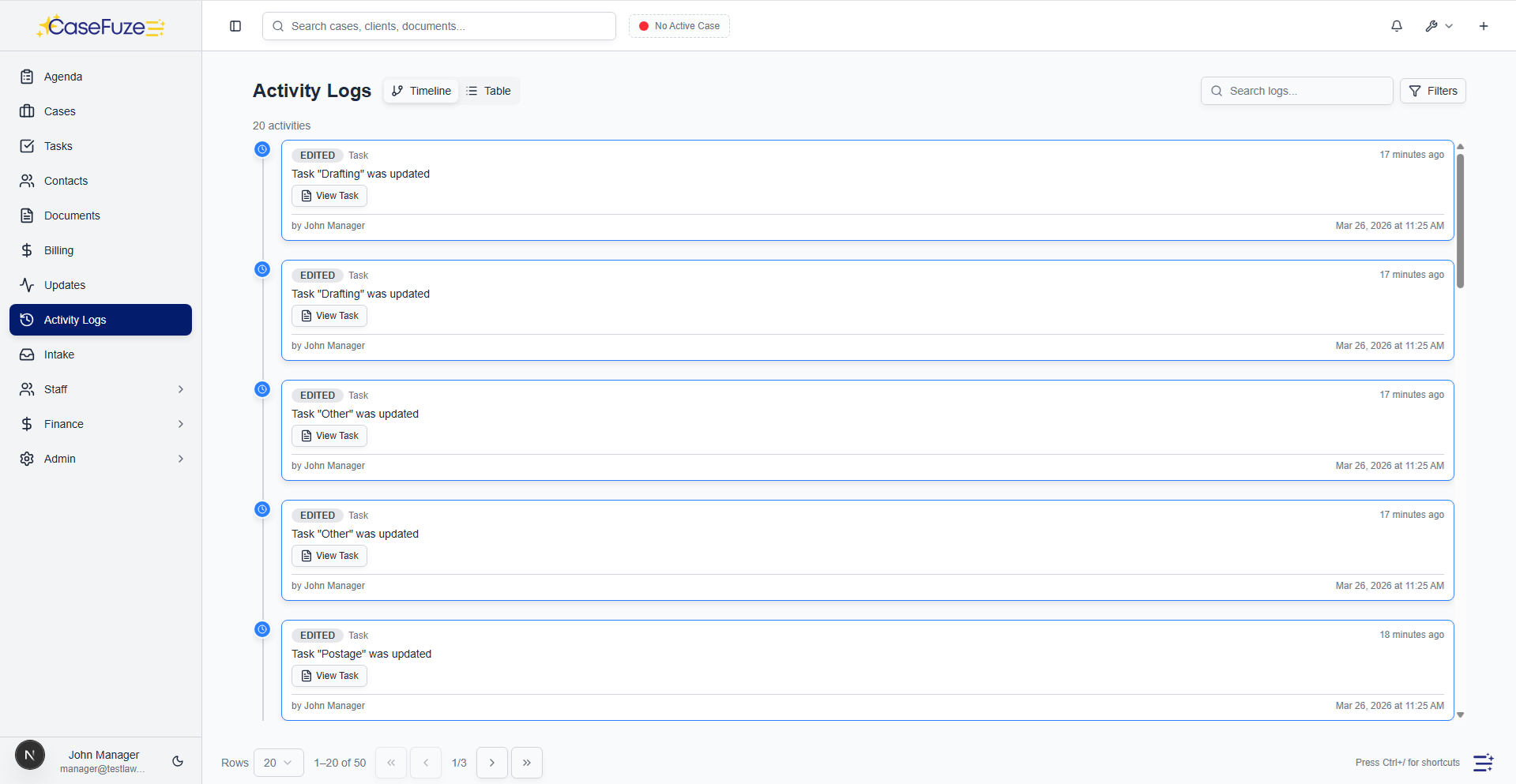
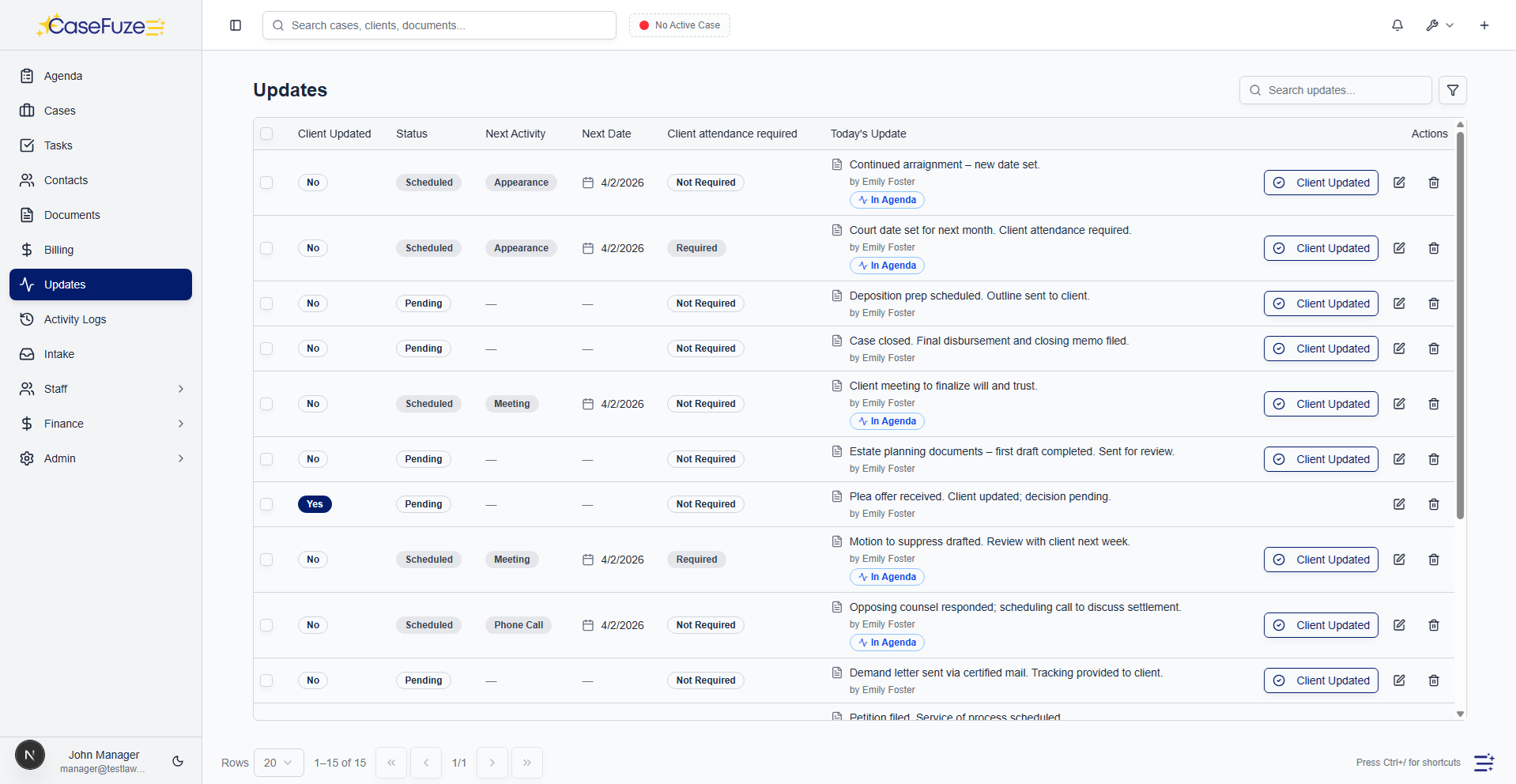
Audit Trails and Logging
Legal ethics and compliance both require being able to show who did what and when.
- User logins and authentication events
- Document uploads, downloads, and deletions
- Case creation, editing, and status changes
Vendor Security
CaseFuze doesn't exist in isolation.
- Amazon Web Services (AWS) for cloud hosting provides SOC 2 certified infrastructure with industry-
- leading security
- Plaid for bank connections maintains SOC 2 compliance and encrypts all financial data
Data Residency and Privacy
Legal data residency requirements vary by jurisdiction.
- Your data is your data we don't claim ownership or licenses beyond what's needed to provide service
- We don't sell data to third parties or use it for purposes beyond operating the platform
- You can export all your data at any time in standard formats
Incident Response
Despite all precautions, security incidents can happen.
- Detection Automated monitoring identifies suspicious activity
- Assessment Security team evaluates severity and scope
- Containment Affected systems isolated to prevent spread
Secure Development Practices
Security starts in how software gets built.
- Code review requirements before any code reaches production
- Automated security testing in continuous integration
- Penetration testing by external security firms